TL;DR
Pre-VAPT helps you understand what to test, why it matters, and where you're exposed before you start a VAPT engagement, so you spend less time on noise and more on real risk.
Introduction
Security teams often treat VAPT (Vulnerability Assessment & Penetration Testing) as the starting point of security.
In reality, VAPT is often the last step — and by the time it begins, critical security blind spots are already baked into the system.
This gap is exactly where Pre-VAPT comes in.
Pre-VAPT is not a replacement for VAPT.
It is a preparatory security intelligence phase that helps organizations understand their true attack surface before expensive and time-bound testing begins.
What Is Pre-VAPT?
Pre-VAPT is the practice of discovering, correlating, and prioritizing security exposure before formal VAPT execution.
It focuses on answering foundational questions such as:
- What exactly should be tested?
- Which assets are actually exposed?
- Where does risk originate — code, dependencies, configs, or cloud?
- What changed since the last VAPT?
Instead of starting with scanning tools or pentests, Pre-VAPT starts with visibility and context.
Core Elements of Pre-VAPT
- Attack surface discovery (code → dependencies → infra → cloud)
- Dependency and supply-chain risk mapping
- Configuration and exposure awareness
- Change detection since last assessment
- Risk prioritization before testing
Why Traditional VAPT Fails Early
Traditional VAPT is extremely valuable — but it fails before it even begins due to structural limitations.
1. Unknown or Incomplete Scope
Most VAPT engagements rely on:
- Manually prepared asset lists
- Outdated architecture diagrams
- Incomplete cloud inventories
You only test what you know — not what actually exists.
Hidden microservices, abandoned APIs, unused subdomains, or transitive dependencies are often never tested.
2. Time-Boxed Testing Misses Deep Risks
VAPT is usually constrained by:
- Fixed timelines
- Fixed budgets
- Fixed scope
As a result:
- Complex dependency chains are ignored
- Misconfigurations are deprioritized
- Low-visibility attack paths are skipped
Critical risks don’t disappear — they’re just postponed.
3. Too Many Findings, Too Little Context
VAPT reports often contain:
- Hundreds of vulnerabilities
- Little correlation to business risk
- No mapping to actual exploit paths
Security teams struggle to answer:
- Which findings matter now?
- Which risks block production?
- Which vulnerabilities are already exploitable?
4. Reactive Instead of Preventive
Traditional VAPT is:
- Periodic (quarterly / yearly)
- Snapshot-based
- Backward-looking
By the time VAPT starts:
- New code is already deployed
- New dependencies are already introduced
- Cloud configurations have already changed
How Pre-VAPT Fixes These Problems
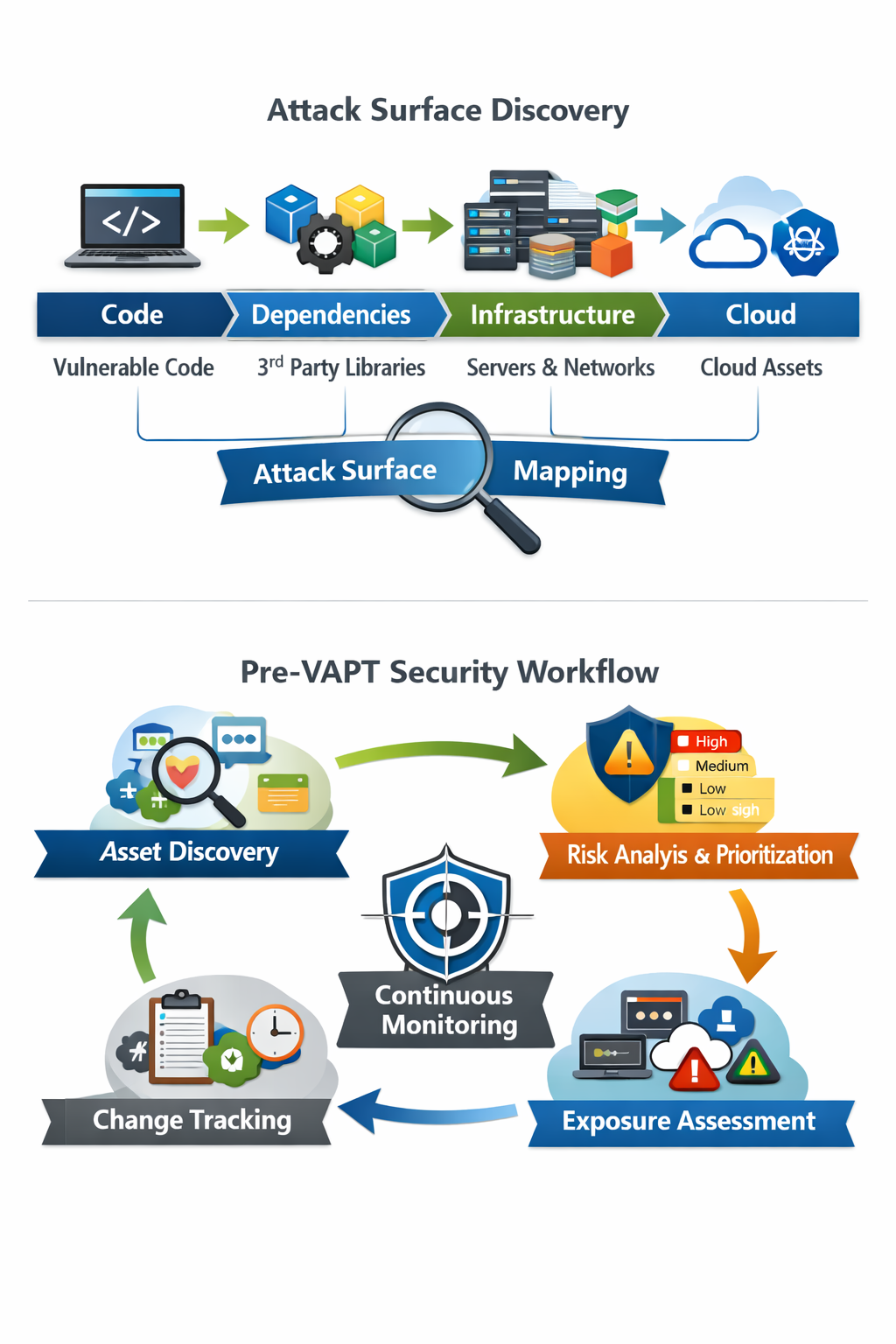 Attack surface discovery and the Pre‑VAPT security workflow from discovery to continuous monitoring.
Attack surface discovery and the Pre‑VAPT security workflow from discovery to continuous monitoring.
1. Accurate, Living Scope Definition
Pre-VAPT automatically discovers:
- Applications and services
- Open ports, APIs, endpoints
- Dependencies and transitive dependencies
- Cloud resources and configurations
VAPT starts with facts, not assumptions.
2. Risk-Driven Testing
Instead of testing everything equally, Pre-VAPT helps:
- Rank assets by exposure
- Identify high-risk components early
- Focus pentesting where it matters most
This leads to:
- Better coverage
- Fewer blind spots
- Lower testing cost
3. Cleaner, Actionable VAPT Reports
When VAPT is informed by Pre-VAPT:
- Findings are contextualized
- Duplicate noise is reduced
- Remediation becomes clearer
Security teams get:
- Fewer findings
- Higher signal-to-noise ratio
- Faster remediation cycles
4. Continuous Readiness, Not One-Time Testing
Pre-VAPT is:
- Continuous
- Change-aware
- Automation-friendly
It allows teams to:
- Detect risk before audits
- Prepare continuously for VAPT
- Reduce last-minute security fire drills
Pre-VAPT vs Traditional VAPT
| Aspect | Traditional VAPT | Pre-VAPT |
|---|---|---|
| Timing | After build/deploy | Before VAPT |
| Scope | Static & manual | Dynamic & discovered |
| Frequency | Periodic | Continuous |
| Focus | Vulnerabilities | Exposure & risk |
| Outcome | Long reports | Prioritized intelligence |
Who Should Care About Pre-VAPT?
Pre-VAPT is especially useful for:
- Product and engineering teams shipping frequently
- Security teams overwhelmed with large VAPT reports
- Cloud-native organizations with many microservices and APIs
- Regulated industries (fintech, healthtech, SaaS) that must prove security posture continuously
If you recognize these patterns in your organization, introducing Pre-VAPT can quickly improve the signal-to-noise ratio of every future VAPT engagement.
Real-World Example
A fintech organization runs annual VAPT.
Without Pre-VAPT:
- 30% of exposed services were out of scope
- Dependency risks were missed
- Cloud misconfigurations were found late
With Pre-VAPT:
- Attack surface was reduced before testing
- VAPT scope was precise
- Findings dropped by 40%
- Fix time reduced significantly
Is Pre-VAPT Replacing VAPT?
No. And it shouldn’t.
Pre-VAPT:
- Makes VAPT more effective
- Makes pentesters more productive
- Makes security teams more confident
Think of it as:
Security intelligence before security testing.
Final Thoughts
Traditional VAPT answers:
“What vulnerabilities exist right now?”
Pre-VAPT answers:
“What should we test, why, and where are we exposed?”
Organizations that adopt Pre-VAPT:
- Spend less on reactive fixes
- Get more value from VAPT
- Reduce unknown risk
How to Get Started with Pre-VAPT
You don’t need a full program redesign to start benefiting from Pre-VAPT. Begin with:
- Inventory what you already expose – apps, APIs, subdomains, cloud accounts.
- Map dependencies and configurations – especially third-party services and cloud defaults.
- Prioritize by business impact and exposure – decide what must be in scope for the next VAPT.
- Feed this context into your VAPT partner or internal red team – so testing effort aligns with real risk.
Even a lightweight Pre-VAPT pass before your next VAPT cycle can make the results dramatically more focused and actionable.
About Xhield
Xhield enables Pre-VAPT by discovering attack surfaces across code, dependencies, infrastructure, and cloud — before formal testing begins.
If VAPT tells you what broke,
Pre-VAPT tells you what will break next.